Anomalous Path Detection
From NUEESS
Jcmartinez (Talk | contribs) (→Extending the BTB) |
Jcmartinez (Talk | contribs) (→Extending the BTB) |
||
| Line 16: | Line 16: | ||
== Extending the BTB == | == Extending the BTB == | ||
| - | [[File: | + | [[File:preditor.png |thumb|right|350px|Microgrid for a community]] |
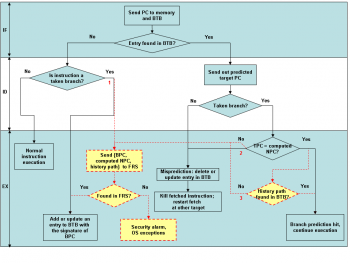
Fig. 4 illustrates the branch prediction flow using a BTB in a simple five-stage pipeline | Fig. 4 illustrates the branch prediction flow using a BTB in a simple five-stage pipeline | ||
architecture. The solid objects and lines are for the regular branch prediction scheme. The | architecture. The solid objects and lines are for the regular branch prediction scheme. The | ||
Revision as of 14:19, 28 March 2012
Contents |
Overview
Program execution can be tampered by malicious attackers through exploiting software vulnerabilities. Changing the program behavior by compromising control data and decision data has become the most serious threat in computer system security. Although several hardware approaches have been presented to validate program execution, they either incur great hardware overhead or introduce false alarms.
We propose a new hardware-based approach by leveraging the existing speculative architectures for run-time program validation. The on-chip branch target buffer (BTB) is utilized as a cache of the legitimate control flow transfers stored in a secure memory region. In addition, the BTB is extended to store the correct program path information. At each indirect branch site, the BTB is used to validate the decision history of previous conditional branches and monitor the following execution path at run-time.
Implementation of this approach is transparent to the upper operating system and programs. Thus, it is applicable to legacy code. Because of good code locality of the executable programs and effectiveness of branch prediction, the frequency of control-flow validations against the secure off-chip memory is low. Our experimental results show a negligible performance penalty and small storage overhead.
Motivation
When control flow attacks are inflicted on a system, the program execution can be directed to either malicious code injected by the attacker or some existing code that would not otherwise execute at that moment. It is the execution of the compromised control instructions that deviate from its expected behavior.
To prevent control flow attacks, our micro-architecture level mechanism validates both control flow transfers and execution paths. The program execution monitoring is sampled at run-time at the sites of indirect branches, instead of every conditional branch or jump. Thus, the performance and storage overhead incurred by the monitoring is reduced greatly. However, since the checking is carried out less frequently, the coverage of each checking process has to be adequate for the program to reduce the false negative rate of validation.
Extending the BTB
Fig. 4 illustrates the branch prediction flow using a BTB in a simple five-stage pipeline architecture. The solid objects and lines are for the regular branch prediction scheme. The flow is also extended with some enhancements for control flow transfer and execution path validation, as shown in dashed lines and objects, which will replace the original operations.
People
Publications
- J. C. Martinez Santos and Y. Fei, “Leveraging speculative architectures for run-time program validation,” in Proc. IEEE Int. Conf. Computer Design, Oct. 2008.
| Whos here now: Members 0 Guests 0 Bots & Crawlers 1 |